
2013 Research
by Dr. Janusz Zalewski
Studying interrelationships of safety and security for software assurance in cyber-physical systems: Approach based on bayesian belief networks
A.J. Kornecki, N. Subramanian, J. Zalewski
Proc. FedCSIS 2013, Federated Conf. on Computer Science and Information Systems, Krakow, Poland, Sept. 8-11, 2013, pp. 1381-1387, 2013.
Abstract: The paper discusses mutual relationships of safety and security properties in cyber-physical systems (CPS). Generally, safety impacts the system's environment while environment impacts security of a CPS. Very frequently, safety and security of a CPS interact with each other either synergistically or conflictingly. Therefore, a combined evaluation of safety and security that considers their interrelationships is required for proper assessment of a CPS. Bayesian Belief Networks (BBN) can be used for this evaluation where factors related to safety and security of a CPS are assumed to be randomly distributed. The result of this evaluation is an assessment that is non-deterministic in nature but gives a very good approximation of the actual extent of safety and security in a CPS. Using a case study of a SCADA system in an oil pipeline control, the authors present a BBN approach for assessing mutual impacts of security and safety violations. This approach is compared with the Non-Functional Requirements approach (NFR), used previously, which is largely qualitative in nature. This study demonstrates that the BBN approach can significantly complement other techniques for joint assessment of safety and security in CPS.
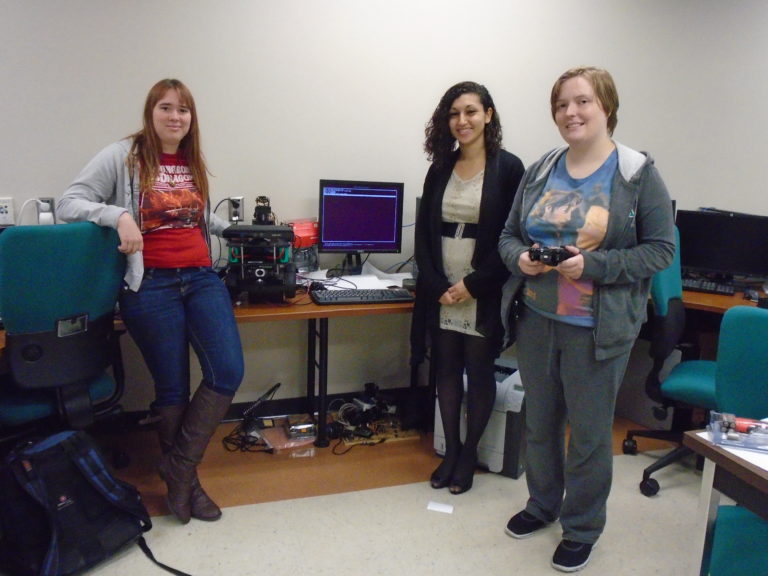
Hands-on Software Engineering Labs via the Web: Game Changing in Online Education
J. Zalewski
TransNav : Intern. Journal on Marine Navigation and Safety of Sea Transportation Vol. 7, No. 2, pp. 243--250, 2013.
Abstract: The paper addresses the issue of offering hands‐on engineering labs via the web. The hands‐on feature refers to the functionality of the lab, which is preserved whether the lab experiments are done over the web or with student’s physical presence in the lab. After an extensive review of remote labs, examples of lab stations are described from the area of software engineering, where software development is done remotely and then software modules are uploaded and tested on the lab stations. This type of lab can be called invasive, since the essential element of an experiment is the replacement or modification of the software module controlling the remote equipment. This is in contrast to regular remote labs, which are non‐invasive. Two lab stations are presented in more detail, one for a wireless sensor network and another for a remotely accessible microcontroller. Several observations are made regarding the usefulness of this technology and prospects of adoption in software engineering programs.
A study of real-time memory management: evaluating operating system's performance
A. Coleman, J. Zalewski
Automatyka/Automatics, Vol. 17, No. 1, 2013.
Abstract: The paper addresses computer memory management with real-time operation in mind. Two essential memory allocation algorithms are analyzed, Hoard and jemalloc, as well as a default algorithm for each specific platform considered. Benchmarking experiments for four platforms, Mac OS X, Linux, Windows NT, and VxWorks, were conducted and respective data collected and analyzed.
